May Cybersecurity Be With You…
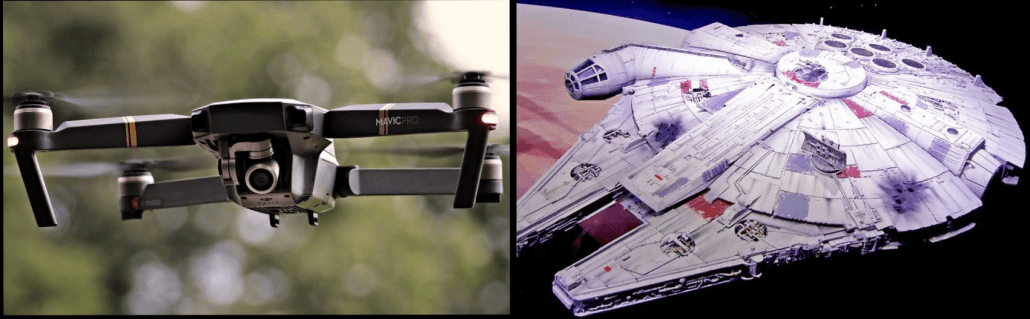
With the VPLS Premiere of Solo: A Star Wars Story fast approaching, there is much hype about finally knowing the origin of Han Solo’s friendship with Lando Calrissian, as well as his companionship with loyal Chewbacca. However, it is futuristic technology such as the iconic Millennium Falcon spacecraft and the intelligent androids that really make the movie; they provide both support and transportation and they look so cool!
So what parallels can be drawn between the Millennium Falcon and our drone technology and cybersecurity?
To find how these two aerial AI-powered vehicles correlate, let’s travel to a galaxy (in a form of a VPLS blog) that is not so far, far away…

The Similarity: The Millennium Falcon and Drones are Droid-Driven!
In the Star Wars franchise, droids [short for androids], are often programmed to carry out particular tasks and regularly have their memories wiped. They are also not being monitored nor are they connected to any network. They are AI at its finest; one is even featured in the upcoming Solo movie serving as Han’s co-pilot of the Millennium Falcon.
The same droid-driven concept is evident through our drone technology today where unmanned aerial vehicles are programmed for agricultural or photography and videography uses, thus becoming more common. And of course in true cybercriminal fashion, as the number of drone technology usage increases, so do the number of attackers accessing the device’s vulnerabilities to read or delete files, or even crash the drone itself.
The Difference: One in Hack-Proof and the Other is Hack-Prone!
Due to the fact that the Millennium Falcon flying droids are not connected to any network, they have a slim to none chance of being hacked. On the other hand, since drones are usually connected to a network like Wi-Fi, they present themselves to be a target for hackers. Their open access points and a misconfigured File Transfer Protocol [FTP} make it possible for a server to overwrite the drone’s remote password file that could lead to an overwrite of the file with a ‘shadow’ file to gain entry.
Once in, the hacker can see what programs are running inside the drone and what devices are connected to its access point. They can also view any active network connections and power it off to block network traffic to halt a user’s viewing experience. Additionally, the attacker could access and download any photos or videos on the drone along with delete files on its SD card without users ever knowing it. The possibilities of what these hackers can do with the user’s information gathered from a drone are endless!
The New Hope: Future of Drone Cyber Security!
In the Star Wars movie series, when the Millennium Falcon needed any maintenance, Han and Chewie fixed it right up. Fortunately, the same can be said for drones and cybersecurity; their manufacturing companies can guard the drone’s access point with a complex password as well as implement tougher encryption standards. Other ways manufacturers can ensure more security for drones include limiting the number of devices that can connect to the same access point, disable its anonymous FTP, and regulate communication between the drone app and the drone itself.
As for now, because these vulnerabilities are ingrained on the drones’ firmware and software, only manufacturers can resolve this matter. Users can only sit tight and trust that companies will take the necessary actions before it escalates into something even more threatening.
But like the majestic Millennium Falcon that always somehow rises to the occasion when Han and his crew are in a crisis, there is always hope that drones will one day be so hack-proof that users could have the opportunity to soar through the skies without a care in any galaxy, whether far, or far, far away…
FOLLOW, LIKE & SHARE VPLS!
If you want to keep up with the latest security trends and other IT related products and services, please visit the VPLS blog and stay current with the latest news!
Don’t forget, VPLS offers Webroot Security Services, an AI driven endpoint security solution that takes a mathematical approach to identify and stop malware in its tracks!